Welcome to your Monday morning digest. As we close out the final full week of April, the global threat landscape is painting a complex picture. We are seeing a volatile mix of deep infrastructure flaws, supply chain risks in remote support software, and a continued, aggressive targeting of emerging AI toolkits.
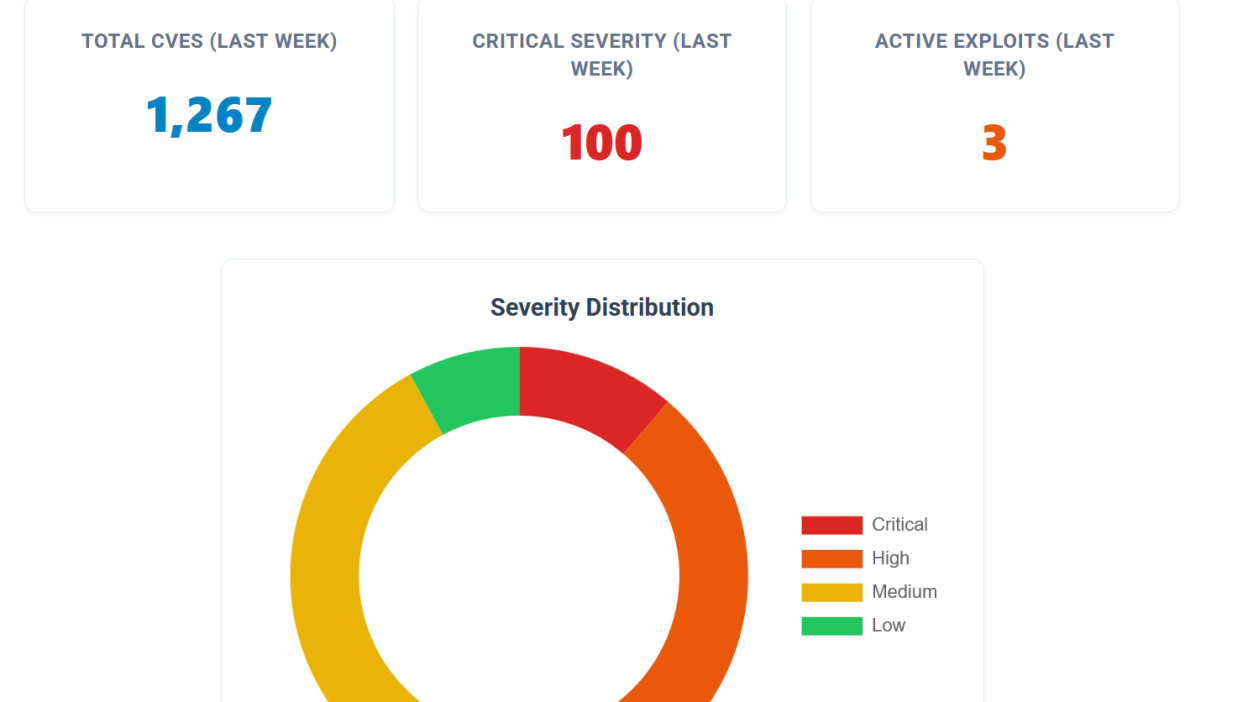
Between April 20 and April 26, 2026, security researchers and vendors published 1,267 new . Whether you are a CISO allocating Q2 defense budgets or an infrastructure engineer prioritizing this week’s patching sprint, here is the curated intelligence you need to stay ahead of the curve.
By the Numbers: The Week at a Glance
Triaging over a thousand vulnerabilities requires cutting through the noise. Here is the severity breakdown of this week’s newly disclosed threats:
- Critical (CVSS 9.0–10.0): 100
- High (CVSS 7.0–8.9): 269
- Medium (CVSS 4.0–6.9): 448
- Low (CVSS 0.1–3.9): 70
- Unknown/Pending Analysis: 379
While 100 Critical is a significant number, the true operational risk lies in the vulnerabilities that threat actors have already weaponized.
The CISA KEV Hotlist: The Supply Chain Strikes Back
The Cybersecurity and Infrastructure Security Agency (CISA) had a remarkably busy week, adding 14 vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog. This week’s KEV additions strongly indicate that attackers are targeting enterprise management and remote support infrastructure to establish initial footholds:
- SimpleHelp Remote Support (CVE-2024-57726 & CVE-2024-57728): Two actively exploited vulnerabilities hit this remote support software. One is a Critical (CVSS 9.9) flaw allowing low-privilege technicians to mint API keys with excessive permissions. The other allows administrators to bypass restrictions and upload arbitrary files directly to the filesystem.
- JetBrains TeamCity (CVE-2024-27199): An actively exploited path traversal vulnerability (CVSS 7.3) allowing limited administrative actions. If your CI/CD pipelines rely on TeamCity, this is a prime target for software supply chain attacks.
- PaperCut NG (CVE-2023-27351): An authentication bypass (CVSS 7.5) in the widely used print management software. Attackers are exploiting this flaw in the
SecurityRequestFilterclass to completely bypass system authentication. - Samsung MagicINFO 9 Server (CVE-2024-7399): A High-severity (CVSS 8.8) directory traversal flaw that permits attackers to write arbitrary files to the server.
In the Wild: Active Exploitation
Beyond the CISA KEV list, our internal Watchtower telemetry flagged three additional, highly diverse threats currently marked as ACTIVE in the wild:
- Breeze Cache for WordPress (CVE-2026-3844): Rated Critical (CVSS 9.8), this plugin flaw allows unauthenticated attackers to execute arbitrary file uploads due to a missing file type validation in the
fetch_gravatar_from_remotefunction. If your marketing team uses Breeze Cache, assume your web perimeter is actively being probed. - LMDeploy AI Toolkit (CVE-2026-33626): LMDeploy is a popular toolkit for compressing and serving Large Language Models (LLMs). An actively exploited Server-Side Request Forgery (SSRF) vulnerability (CVSS 7.5) is currently being leveraged to attack internal infrastructure hosting these models.
- D-Link DIR-823X Routers (CVE-2025-29635): An authorized attacker can leverage a command injection vulnerability (CVSS 8.8) to execute arbitrary commands on remote networking devices, a classic vector for botnet expansion.
The Maximum Severity Flaw
A CVSS score of 10.0 is the cybersecurity equivalent of a five-alarm fire: trivial to exploit, network-exploitable, requiring zero authentication, and resulting in total system compromise. Keep a close eye on these maximum-severity disclosures:
- Paperclip AI Orchestrator (CVE-2026-41679): Paperclip is a Node.js server used to orchestrate teams of AI agents. Prior to version 2026.416.0, an unauthenticated attacker can completely compromise the server. This marks the second week in a row where core AI orchestration infrastructure has suffered a CVSS 10.0 vulnerability.
- OpenVPN Authentication Plugin (CVE-2026-41070): When the
openvpn-auth-oauth2plugin is deployed in its experimental shared library mode, it suffers a catastrophic vulnerability allowing total compromise of the VPN gateway. - Perl Library Flaws (CVE-2025-15638 & CVE-2017-20230): Two CVSS 10.0 bugs surfaced impacting Perl modules. One involves a vulnerable version of
libtomcryptbundled insideNet::Dropbear, and the other is a legacy stack overflow in theStorablemodule. - WWBN AVideo (CVE-2026-40911): An open-source video platform flaw where the YPTSocket WebSocket server blindly relays attacker-supplied JSON messages, leading to full system compromise.
The Bottom Line
For the System Administrators and Engineers: Your immediate priority is locking down remote access and CI/CD tools. Check your networks for SimpleHelp installations and ensure your JetBrains TeamCity servers are fully patched. After securing the infrastructure, sweep your WordPress instances for the Breeze Cache plugin.
For the CISOs and Security Directors: The threat data over the last two weeks is telling a very clear story—AI infrastructure is under siege. From last week’s attacks on MCP adapters to this week’s active exploitation of the LMDeploy toolkit and the CVSS 10.0 in Paperclip AI orchestration, threat actors are heavily pivoting toward the AI supply chain. You must ensure your DevSecOps teams are auditing their LLM deployment pipelines with the same rigor applied to your most critical, public-facing web applications.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.