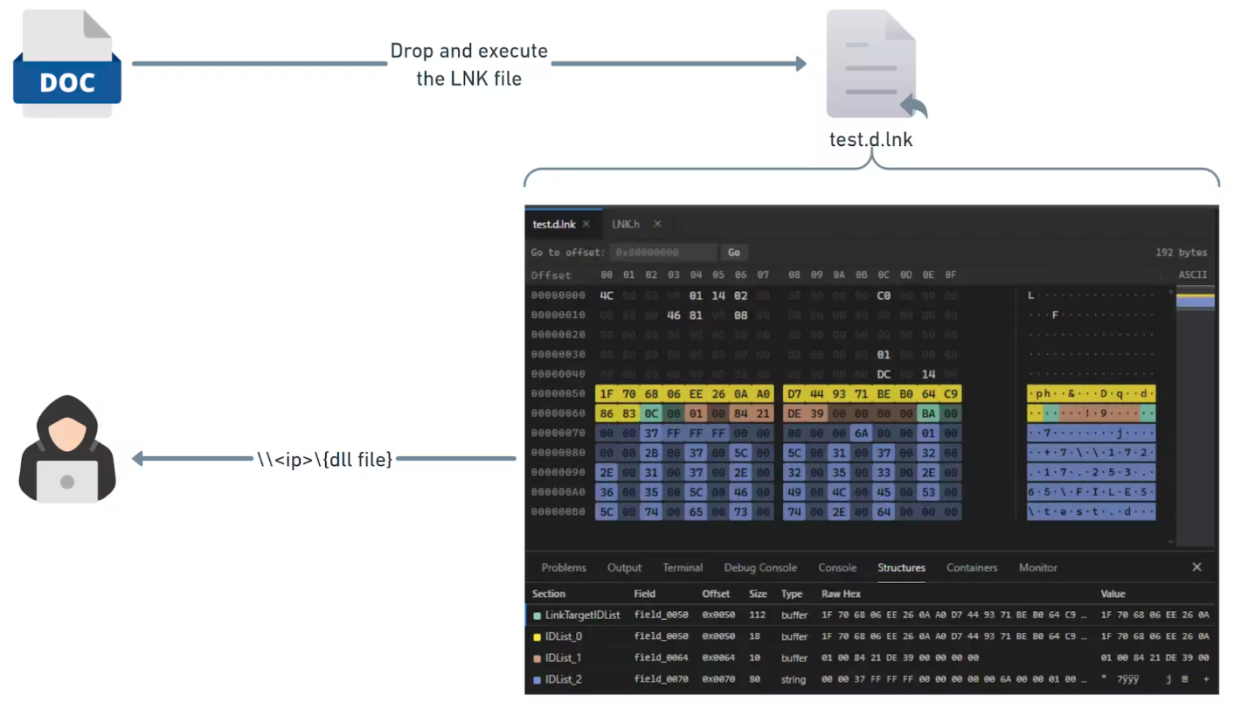
Conceptual flow of the original CVE-2026-21510 exploitation | Image: Akamai
Researchers at Akamai have discovered that a previous fix for a high-profile exploit used by the Russian-linked group APT28 (also known as Fancy Bear) was incomplete. This oversight has birthed a new, “zero-click” —tracked as CVE-2026-32202—that allows for silent credential theft without a single interaction from the victim.
The saga began in late 2025, when APT28 launched a campaign targeting Ukraine and several EU countries. They utilized a weaponized LNK file to exploit a critical remote code execution (RCE) . While Microsoft’s subsequent patch on February’s Patch Tuesday successfully blocked the RCE and a related SmartScreen bypass, it failed to address the underlying mechanism of how Windows handles these files.
As the Akamai report explains, “While Microsoft’s fix successfully prevented the initial remote code execution (RCE) and SmartScreen bypass, it left behind a zero-click authentication coercion vulnerability”.
The vulnerability is activated the moment a user simply navigates to a folder containing the malicious LNK file. When Windows Explorer renders the folder contents, it automatically attempts to extract an icon for the items inside. This process triggers a call chain that causes Windows to resolve a UNC path pointing to an attacker-controlled server.
The report details the technical chain reaction: “The PathFileExistsW call… is the earliest trigger, which causes Windows to resolve the UNC path and initiate an SMB connection. This happens the moment Explorer renders the folder contents, without any user click”.
This automatic connection triggers an NTLM authentication handshake, effectively handing the victim’s Net-NTLMv2 hash directly to the attacker. These hashes can then be cracked offline or reused in relay attacks to gain further access to the network.
Until a comprehensive fix is fully integrated and deployed, administrators should treat LNK files with heightened suspicion. Organizations are encouraged to monitor for unusual SMB connections to external or unknown IP addresses and ensure that NTLM protections are strictly enforced.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.